9.1 KiB
| layout | page_title | sidebar_current | description |
|---|---|---|---|
| registry | Terraform Registry - Publishing Providers | docs-registry-provider-publishing | Publishing Providers to the Terraform Registry |
Publishing Providers
Anyone can publish and share a provider by signing into the Registry using their GitHub account and following a few easy steps.
This page describes how to prepare a Terraform Provider for publishing, and how to publish a prepared provider using the Registry's interface.
Preparing your Provider
Writing a Provider
Providers published to the Terraform Registry are written and built in the same way as other Terraform providers. A variety of resources are available to help our contributors build a quality integration:
- The Call APIs with Terraform Providers collection on HashiCorp Learn
- How to build a provider – Video
- Sample provider developed by a HashiCorp partner
- Example providers for reference:
- Contributing to Terraform guidelines
~> Important: In order to be detected by the Terraform Registry, all provider repositories on GitHub must match the pattern terraform-provider-{NAME}, and the repository must be public.
Documenting your Provider
Your provider should contain an overview document (index.md), as well as a doc for each resource and data-source. See Documenting Providers for details about how to ensure your provider documentation renders properly on the Terraform Registry.
-> Note: In order to test how documents will render in the Terraform Registry, you can use the Terraform Registry Doc Preview Tool.
Creating a GitHub Release
Publishing a provider requires at least one version be available on GitHub Releases. The tag must be a valid Semantic Version preceded with a v (for example, v1.2.3).
Terraform CLI and the Terraform Registry follow the Semantic Versioning specification when detecting a valid version, sorting versions, solving version constraints, and choosing the latest version. Prerelease versions are supported (available if explicitly defined but not chosen automatically) with a hyphen (-) delimiter, such as v1.2.3-pre.
We have a list of recommend OS / architecture combinations for which we suggest most providers create binaries.
~> Important: Avoid modifying or replacing an already-released version of a provider, as this will cause checksum errors for users when attempting to download the plugin. Instead, if changes are necessary, please release as a new version.
GitHub Actions (Preferred)
GitHub Actions allow you to execute workflows when events on your repository occur. You can use this to publish provider releases to the Terraform Registry whenever a new version tag is created on your repository.
To use GitHub Actions to publish new provider releases to the Terraform Registry:
- Create and export a signing key that you plan on using to sign your provider releases. See Preparing and Adding a Signing Key for more information.
- Copy the GoReleaser configuration from the terraform-provider-scaffolding repository to the root of your repository.
- Copy the GitHub Actions workflow from the terraform-provider-scaffolding repository to
.github/workflows/release.ymlin your repository. - Go to Settings > Secrets in your repository, and add the following secrets:
GPG_PRIVATE_KEY- Your ASCII-armored GPG private key. You can export this withgpg --armor --export-secret-keys [key ID or email].PASSPHRASE- The passphrase for your GPG private key.
- Push a new valid version tag (e.g.
v1.2.3) to test that the GitHub Actions releaser is working.
Once a release is created, you can move on to Publishing to the Registry.
Using GoReleaser locally
GoReleaser is a tool for building Go projects for multiple platforms, creating a checksums file, and signing the release. It can also upload your release to GitHub Releases.
- Install GoReleaser using the installation instructions.
- Copy the .goreleaser.yml file from the hashicorp/terraform-provider-scaffolding repository.
- Cache the password for your GPG private key with
gpg --armor --detach-sign(see note below). - Set your
GITHUB_TOKENto a Personal Access Token that has the public_repo scope. - Tag your version with
git tag v1.2.3. - Build, sign, and upload your release with
goreleaser release --rm-dist.
-> GoReleaser does not support signing binaries with a GPG key that requires a passphrase. Some systems may cache your GPG passphrase for a few minutes. If you are unable to cache the passphrase for GoReleaser, please use the manual release preparation process below, or remove the signature step from GoReleaser and sign it prior to moving the GitHub release from draft to published.
Manually Preparing a Release
If for some reason you're not able to use GoReleaser to build, sign, and upload your release, you can create the required assets by following these steps, or encode them into a Makefile or shell script.
The release must meet the following criteria:
- There are 1 or more zip files containing the built provider binary for a single architecture
- The binary name is
terraform-provider-{NAME}_v{VERSION} - The archive name is
terraform-provider-{NAME}_{VERSION}_{OS}_{ARCH}.zip
- The binary name is
- There is a
terraform-provider-{NAME}_{VERSION}_SHA256SUMSfile, which contains a sha256 sum for each zip file in the release.shasum -a 256 *.zip > terraform-provider-{NAME}_{VERSION}_SHA256SUMS
- There is a
terraform-provider-{NAME}_{VERSION}_SHA256SUMS.sigfile, which is a valid GPG signature of theterraform-provider-{NAME}_{VERSION}_SHA256SUMSfile using the keypair.gpg --detach-sign terraform-provider-{NAME}_{VERSION}_SHA256SUMS
- Release is finalized (not a private draft).
Publishing to the Registry
Signing in
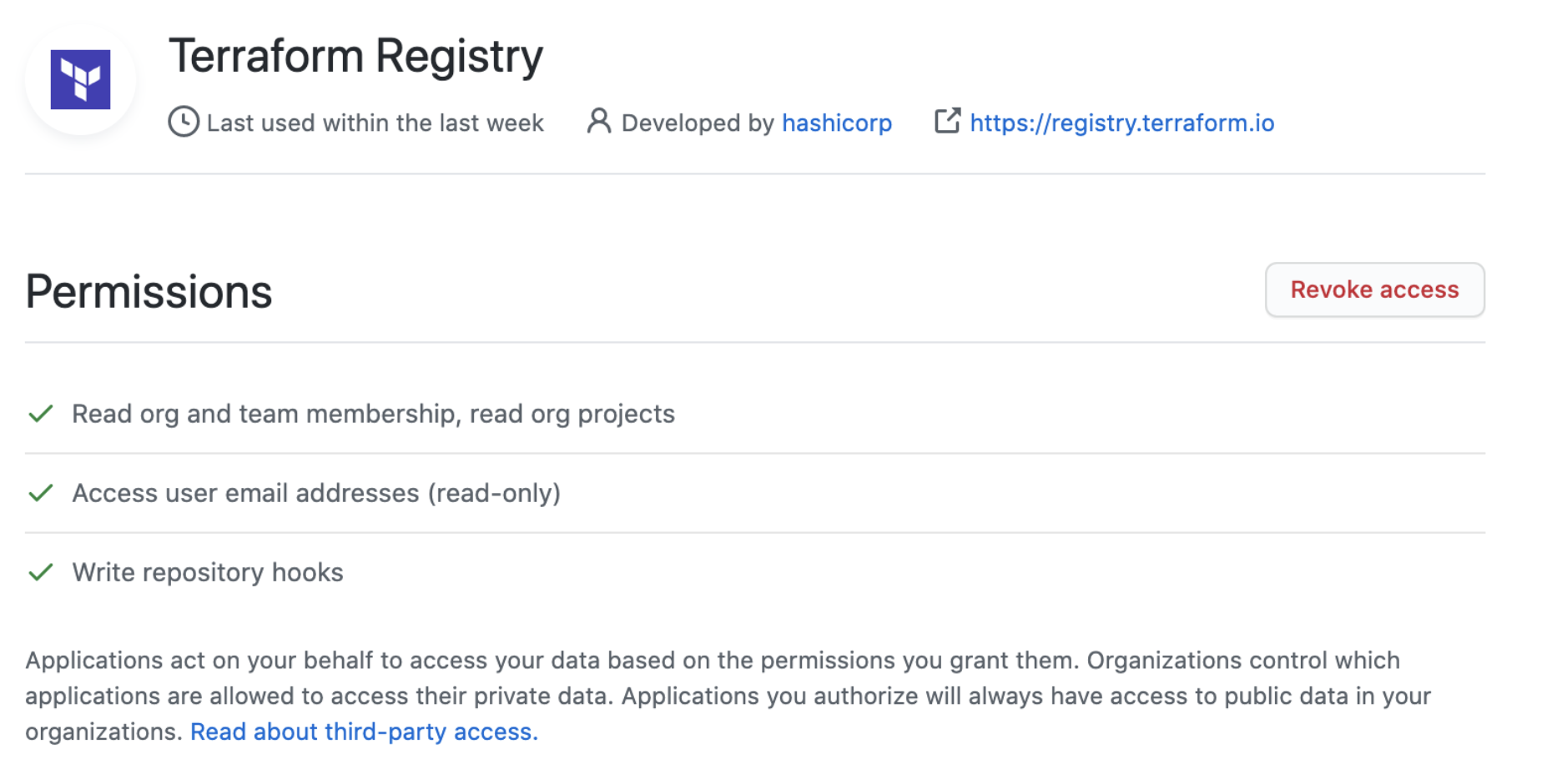
Before publishing a provider, you must first sign in to the Terraform Registry with a GitHub account (see Signing into the Registry). The GitHub account used must have the following permission scopes on the provider repository you’d like to publish. Permissions can be verified by going to your GitHub Settings and selecting the Terraform Registry Application under Authorized OAuth Apps.
Preparing and Adding a Signing Key
All provider releases are required to be signed, thus you must provide HashiCorp with the public key for the GPG keypair that you will be signing releases with. The Terraform Registry will validate that the release is signed with this key when publishing each version, and Terraform will verify this during terraform init.
- Generate a GPG key to be used when signing releases (See GitHub's detailed instructions for help with this step, but you do not need to add the key to GitHub)
- Export your public key in ASCII-armor format using the following command, substituting the GPG key ID created in the step above:
$ gpg --armor --export "{Key ID or email address}"
The ASCII-armored public key to the Terraform Registry by going to User Settings > Signing Keys. You can add keys for your personal namespace, or any organization which you are an admin of.
Publishing Your Provider
In the top-right navigation, select Publish > Provider to begin the publishing process. Follow the prompts to select the organization and repository you would like to publish.
Terms of Use
Anything published to the Terraform Registry is subject to our terms of use. A copy of the terms are available for viewing at https://registry.terraform.io/terms
Support
If you experience issues publishing your provider to the Terraform Registry, please contact us at terraform-registry@hashicorp.com.